Sleeper cell warnings intensify during geopolitical crises not because threats materialize but because security states need domestic anxiety to justify power.
Geopolitical Crises Are Domestic Power Grabs
Moments of geopolitical escalation never stay confined to foreign policy. When states go to war, conflict immediately becomes domestic. Political leaders warn of retaliation. Intelligence agencies issue alerts. Media coverage pivots toward the threat at home. This is visible now as U.S. military strikes on Iran produce warnings about Iranian sleeper cells already operating inside the United States — federal agencies issuing threat bulletins, drone attack scenarios circulating through press briefings, scattered security incidents absorbed into a coherent national danger narrative.
None of this is incidental. It is the security state functioning exactly as designed. The foreign war and the domestic crackdown are not separate events that happen to coincide — they are the same project, operating on two fronts simultaneously. Understanding sleeper cell warnings requires understanding what they are structurally built to accomplish, not just what they claim to describe.
Problem, Reaction, Solution — Every Time
The basic logic of security state expansion follows a predictable sequence. A threat is identified or amplified. Public anxiety rises. Authorities present expanded powers as the necessary response. Scrutiny of whether those powers are legitimate, proportionate, or even effective gets drowned out by the urgency of the crisis moment. This sequence does not require conspiracy to function. It requires only that institutions with a direct interest in expanded authority be the ones narrating the threat environment.
When an attack occurs — or when the credible possibility of one is elevated into public consciousness — the political question immediately becomes: how did we fail to stop this? That framing presupposes the answer. The failure was insufficient power. Not wrong priorities. Not manufactured pretexts. Not wars of aggression that created the conditions for blowback. The solution is always the same: more surveillance, broader legal authority, fewer constraints on intelligence agencies, faster pathways from monitoring to detention.
Not a Conspiracy — A Feature of How States Work
None of this requires a secret coordinating body. No smoke-filled room. No unified chain of command issuing orders to manufacture threats. That is precisely the point. The security state does not need conspiracy to function this way — it needs only its own institutional logic, operating normally, as designed. Describing this as a structural dynamic is not a softer claim than calling it a conspiracy. It is a more damning one. Conspiracies can be exposed and dismantled. Structural imperatives reproduce themselves regardless of which individuals occupy positions of power.
The sociologist Max Weber defined the state by its claim to a monopoly on the legitimate use of physical force within a given territory. This is the foundational insight that security state behavior in crisis moments makes legible. The monopoly on violence is not simply about who can physically coerce whom — it is about who controls the definition of legitimate threat, legitimate response, and legitimate force. When the state identifies a sleeper cell, it is not only naming a danger. It is asserting its exclusive authority to define what danger is, who embodies it, and what measures are warranted in response. All competing definitions — community self-determination, political dissent, civil liberties claims — are subordinated to that monopoly.
Weber’s framework also explains why the expansion of security power is self-reinforcing rather than self-correcting. Every challenge to state authority — every attack, every incident, every foreign adversary — becomes an occasion to reassert and extend the monopoly. The state does not respond to threats by sharing power or devolving authority. It responds by concentrating both. Geopolitical crisis accelerates this dynamic because it provides the legitimating condition the state most depends on: the existence of an enemy whose threat justifies whatever is being asked of the population in exchange for protection. The Iran war, and the sleeper cell warnings that followed within days, follow this logic with textbook precision.
Ottawa 2014: The Script Runs in Real Time
The October 2014 attack on Parliament Hill is among the clearest modern examples of this dynamic playing out in Canadian politics. Michael Zehaf-Bibeau was known to multiple intelligence and law enforcement agencies before he opened fire inside Centre Block. RCMP, CSIS, and passport officials had all flagged him. He was already in the system.
What is critical to understand is what was happening in Ottawa at the moment of the attack: Parliament was actively debating the expansion of CSIS powers. Bill C-44 was already in progress, and the Conservative government under Stephen Harper was pushing to broaden the legal authority of Canadian intelligence services. The attack did not interrupt that debate. It ended it. Within weeks, the government introduced Bill C-51 — sweeping anti-terrorism legislation that dramatically expanded CSIS’s mandate to act, not just collect, and made it easier to detain, surveil, and disrupt individuals without criminal charges. The public question — how could they let this happen? — was answered before it could be fully asked: they didn’t have enough power. Give them more.
The legal constraints that supposedly prevented earlier intervention were never the reason Zehaf-Bibeau wasn’t stopped. They were the pretext that made his attack politically useful. The security state had been watching him. It had the information. What it wanted was the authority to act on that kind of information without the evidentiary standards that criminal law requires — the ability to detain, disrupt, and monitor at scale, with judicial oversight reduced to a formality. Parliament Hill handed them the argument.
Preemption Logic Makes Every Attack a Justification
Modern security institutions are built on the logic of anticipatory threat. Intelligence agencies do not wait for crimes to be committed — they identify, monitor, and track individuals assessed as potentially dangerous. NIJ data shows 61.56 percent of domestic terrorists between 2001 and 2020 had prior contact with law enforcement or security institutions before their attacks. They were known. They were watched. And when they acted, the institutional response was not to ask whether the surveillance framework failed — but to demand that it be expanded.
This is the permanent trap built into preemption logic. If an attack happens and the perpetrator was already known, the argument is that agencies needed more authority to act earlier. If an attack happens and the perpetrator was unknown, the argument is that agencies needed broader surveillance to have found them. Either outcome justifies expansion. There is no result — no attack, no non-attack, no intelligence success, no intelligence failure — that the security state cannot convert into an argument for more power. The logic is self-sealing.
Sleeper Cell Warnings Are Infrastructure, Not Intelligence
When federal officials warn of Iranian sleeper cells activating inside the United States, they are not primarily communicating a specific, assessed threat. They are doing something more structural: conditioning the public to accept that the domestic population contains hidden enemies, that normal legal standards are inadequate to address them, and that security agencies must operate with greater latitude to find and neutralize threats before they materialize.
Sleeper cell framing is particularly effective because it renders the absence of evidence into evidence of sophistication. If no attack has occurred, that proves the cells are dormant and patient — which makes them more dangerous, not less. If an incident does occur, it confirms what authorities warned. The concept is unfalsifiable by design. It produces permanent justification for permanent surveillance, independent of whether any actual network exists or poses any actual threat.
This is not incidental to how security agencies communicate. It is the point. The Garland, Texas case — where the FBI had monitored the attacker for years and had an undercover agent in a car directly behind the shooters when the first shots were fired — illustrates what active security apparatus presence actually looks like. The question of why that monitoring did not produce intervention is not answered by calls for more authority. It is answered by recognizing that monitoring and intervention are different institutional projects, serving different political functions.
War Manufactures the Threat It Claims to Contain
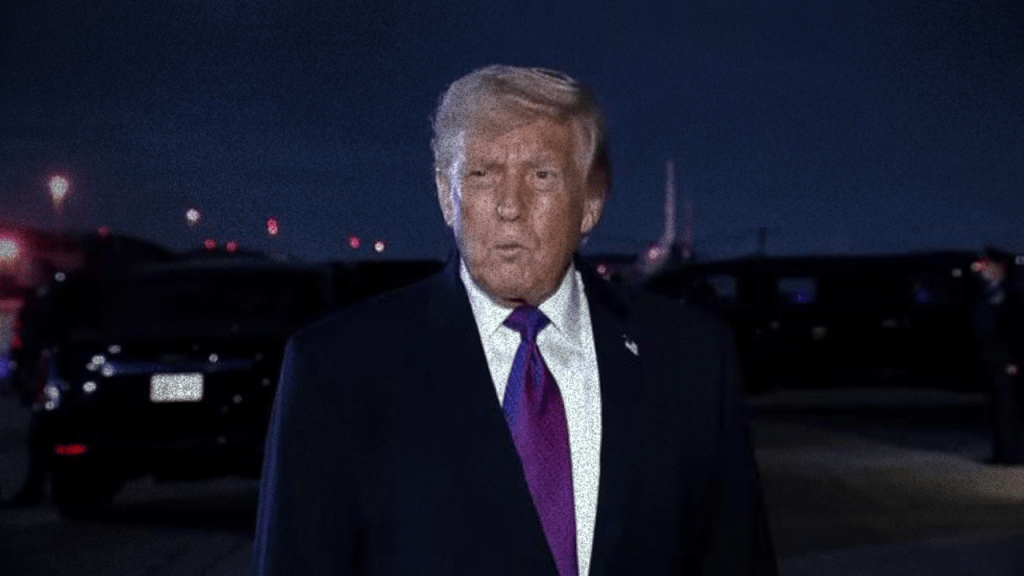
The current context makes this dynamic impossible to separate from the war itself. The United States launched Operation Epic Fury against Iran on February 28, 2026. The strikes were framed as targeting nuclear infrastructure and eliminating an existential threat. Within days, the domestic threat narrative was already operational: Iranian networks inside the country, sleeper cells awaiting activation, critical infrastructure at risk.
This sequence cannot be treated as coincidental. A war of aggression against a nation-state generates real conditions for blowback — not because Iran is a uniquely dangerous adversary, but because that is what wars do. They create grievances, they activate networks, they give political and material reasons for retaliation. The security state then uses those conditions — conditions it helped manufacture through the war — to justify the very expansion of domestic authority it was already pursuing. The threat is real enough to be credible, and was made real by policy choices that the same political actors now claim to be protecting the public from.
This is the full loop. Military aggression abroad produces threat conditions at home. Threat conditions at home justify expanded surveillance and police power. Expanded surveillance and police power position the security state to manage the next crisis — and the crisis after that. The population is kept in a permanent state of managed anxiety, in which the institutions responsible for producing the danger are also the only ones with the authority to address it.
Historical Deception Is the Context, Not a Caveat
Skepticism toward these narratives is not paranoia — it is the appropriate response to documented institutional behavior. The Gulf of Tonkin incident, used to justify expanded U.S. military involvement in Vietnam, was built on an attack that NSA documents confirmed never occurred. The 2003 invasion of Iraq was justified by weapons of mass destruction claims that the Iraq Survey Group found no evidence to support. MKUltra was real — illegal human experimentation conducted by the CIA from 1953 to 1973, concealed for decades and only partially revealed through congressional investigation.
These are not ancient history deployed to discredit contemporary institutions by association. They are the evidentiary basis for treating security state claims as claims requiring scrutiny — not as baseline truth that gets modified only when proven false. The burden of proof runs the other way. Institutions with this track record, making these arguments, at this moment, in the middle of a war they launched, do not deserve the benefit of the doubt as a default posture.
The Institutions Manufacturing Crisis Never Change
Sleeper cell warnings during the Iran war are not an anomaly produced by unusual danger. They are a standard-issue instrument of security state governance, deployed on schedule, serving their intended function. The threat may be partly real — wars produce real instability. But the political use of that threat is not about public safety. It is about power: who has it, who is expanding it, and who is being conditioned to accept its expansion as necessary and inevitable.
The Parliament Hill attack did not create the appetite for C-51. It provided the occasion. The Iran war did not create the appetite for expanded domestic surveillance and reduced civil liberties constraints. It provided the occasion. The institutions running this cycle — military, intelligence, political — remain constant across administrations, across borders, across decades. What changes is only the specific threat being named. The script does not.
Sources
- ABC News — Iran may be activating sleeper cells outside the country, March 9, 2026
- Newsweek — Iran War: New Alert Warns of Sleeper Cells Activating, March 9, 2026
- National Institute of Justice — Domestic Terrorists’ Contact with System Stakeholders Before Attacks
- CBS News — Terrorism in Garland, Texas: What the FBI Knew
- U.S. Naval Institute — The Truth About Tonkin
- PBS NewsHour — Report Finds No WMD in Iraq
- NPR — The CIA’s Secret Quest For Mind Control